Hacking Tools are programs designed to find and exploit weaknesses in computer systems, web applications, servers, and networks.
Hacking tools have made the task of the hackers much simpler when compared to the times they did not exist.
But it does not mean that if the Hacker is equipped with good Hacking Tools, his entire job is smoothly done. The hacker still requires the skills of all the aspects of hacking equally well.
In past decades, ethical hacking and penetration testing were performed by only a few security experts.
Now almost anyone can report security incidents. Ethical hacking and online security involve a lot of effort.
Many hacking tools are used to test and keep the software secure. The same hacking tools can also be used by hackers for exploitation.
Top 15 Best Hacking Tools For Ethical Hackers
1. Nmap

Nmap stands for Network Mapper. This Hacking Tool is open-source software that is used widely for network discovery and security auditing.
Nmap was originally designed to scan large networks, but it can work equally well for single hosts.
Network administrators also find it useful for tasks such as network inventory, managing service upgrade schedules, and monitoring host or service uptime.
Features:
- what hosts are available on the network,
- what services those hosts are offering,
- what operating systems they are running on,
- what type of firewalls are in use and other such characteristics.
- Nmap runs on all major computer operating systems such as Windows, Mac OS X, and Linux.
2. Netsparker
Netsparker Hacking Tool is an easy-to-use web application security scanner software that can automatically find SQL Injection, XSS, and other vulnerabilities in your web applications and web services. The Hacking Tool is available as an on-premises and SAAS solution.
Features:
- Dead accurate vulnerability detection with the unique Proof-Based Scanning Technology.
- A minimal configuration is required. The scanner automatically detects URL rewrite rules, and custom 404 error pages.
- REST API for seamless integration with the SDLC, and bug tracking systems.
- Fully scalable solution. Scan 1,000 web applications in just 24 hours.
3. Metasploit

Metasploit is one of the most powerful hacking tools. Metasploit Hacking Tool is an open-source cyber-security project that allows infosec professionals to use different penetration testing tools to discover remote software vulnerabilities.
It comes in two versions − commercial and free edition. Metasploit Hacking Tool can be used with the command prompt or with Web UI.
Features:
- Conduct basic penetration tests on small networks
- Run spot checks on the exploitability of vulnerabilities
- Discover the network or import scan data
- Browse exploit modules and run individual exploits on hosts
4. Aircrack-Ng

Aircrack-ng provides different hacking tools for evaluating Wi-Fi network security. All are command-line tools. For Wi-Fi security.
The Hacking Tool focuses on monitoring, attacking, testing, and cracking. It supports Linux, Windows, OS X, Free BSD, NetBSD, OpenBSD, Solaris, and eComStation 2.
Features:
- Aircrack-ng can focus on Replay attacks, de-authentication, fake access points, and others.
- It supports exporting data to text files.
- It can check Wi-Fi cards and driver capabilities.
- It can crack WEP keys and for that, it makes use of FMS attacks, PTW attacks, and dictionary attacks.
- It can crack WPA2-PSK and for that, it makes use of dictionary attacks.
5. Cain & Abel Hacking Tools
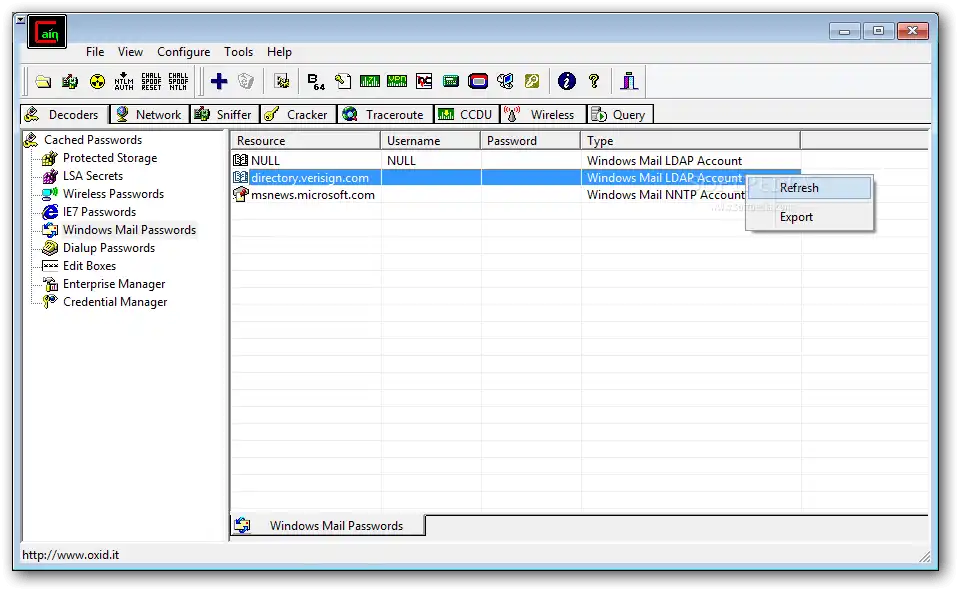
Cain & Abel is a password recovery hacking tool for Microsoft Operating Systems. This hacking tool has the capability to recover various kinds of passwords using techniques such as cracking the password hashes by using brute-forcing, dictionary attacks, cryptanalysis attacks, and packet sniffing in the network.
Cain & Abel is a useful hacking tool for security consultants, professional penetration testers, and everyone else who plans to use it for ethical reasons.
Features:
- sniffing the network,
- racking encrypted passwords using Dictionary, Brute-Force, and Cryptanalysis attacks,
- recording VoIP conversations,
- decoding scrambled passwords,
- recovering wireless network keys,
- revealing password boxes,
- uncovering cached passwords and analyzing routing protocols.
6. Nikto
Nikto is another favorite, well-known hacking tool as part of the Kali Linux Distribution.
Other popular Linux distributions such as Fedora already come with Nikto available in their software repositories as well.
This security tool is used to scan web servers and perform different types of tests against the specified remote host.
The Hacking Tool is a clean and simple command-line interface that makes it really easy to launch any vulnerability testing against your target.
Features:
- Detects default installation files on any OS
- Detects outdated software applications.
- Runs XSS vulnerability tests
- Launches dictionary-based brute force attacks
- Exports results in plain text, CSV, or HTML files
- Intrusion detection system evasion with LibWhisker
- Integration with Metasploit Framework
7. Ettercap
Ettercap is a Hacking Tool that supports cross-platform. Using Ettercap’s API, you can create custom plugins.
Even with the proxy connection, this hacking software can do sniffing of HTTP SSL secured data. Ettercap Hacking Tool is a free and open-source network security hacking tool for man-in-the-middle attacks on LAN.
This hacking tool can be used for computer network protocol analysis and security auditing. It runs on various Unix-like operating systems including Linux, Mac OS X, BSD, and Solaris, and on Microsoft Windows.
Features:
- Sniffing of live connections.
- Content filtering.
- Active and passive dissection of many protocols.
- Network and host analysis.
8. SuperScan
SuperScan Hacking Tool is a powerful hacking software for network administrators to scan TCP ports and resolve hostnames.
SuperScan is a free connect-based port scanning software designed to detect open TCP and UDP ports on a target computer, determine which services are running on those ports, and run queries such as whois, ping, and ICMP traceroute, and Hostname lookups.
Perform ping scans and port scans using any IP range.
Features:
- Perform ping scans and port scans using any IP range.
- can any port range from a built-in list or any given range.
- View responses from connected hosts.
- Modify the port list and port descriptions using the built-in editor.
- Merge port lists to build new ones.
- Connect to any discovered open port.
- Assign a custom helper application to any port.
9. Maltego

Maltego is a hacking tool for link analysis and data mining. This hacking tool is an open-source forensic and intelligence software used for gathering information in all phases of security-related work. This Hacking Tool saves your time and money by performing the task on time in a smarter way.
For the discovery of data from open sources and visualizing the information in graphical format, This hacking tool provides a library of transforms.
The Hacking Tool performs real-time data-mining and information gathering. this hacking tool can work with very large graphs. The Hacking Tool also supports Windows, Linux, and Mac OS.
Features:
- Represents the data on node-based graph patterns.
- Maltego XL can work with large graphs.
- It will provide you a graphical picture, thereby telling you about the weak points and abnormalities of the network.
10. Wireshark
Wireshark Hacking Tool is a free and open-source packet analyzer software. This hacking tool is used for network troubleshooting, analysis, software and communications protocol development, and education.
This Hacking tool lets you see what’s happening on your network at a microscopic level and is the de facto (and often de jure) standard across many commercial and non-profit enterprises, government agencies, and educational institutions.
Features:
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane packet browser
- Multi-platform: Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be browsed via a GUI, or via the TTY-mode TShark utility
- The most powerful display filters in the industry
- Rich VoIP analysis
- Capture files compressed with gzip can be decompressed on the fly
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Coloring rules can be applied to the packet list for quick, intuitive analysis
- Output can be exported to XML, PostScript®, CSV, or plain text
11. John The Ripper
John the Ripper is a hacking tool for password cracking. This hacking tool can be used on Windows, DOS, and Open VMS.
The Hacking Tool is an open-source hacking tool. This Hacking Tool is created for detecting weak UNIX passwords.
This Hacking Tool has the capability to combine several password crackers into a single package which has made it one of the most popular cracking tools for hackers.
Features:
- Features: John the Ripper can be used to test various encrypted passwords.
- It performs dictionary attacks.
- It provides various password crackers in one package.
- It provides a customizable cracker.
- Best For: It is fast in password cracking.
12. Angry IP Scanner

Angry IP Scanner hacking software is a fast port and IP address scanner. This Hacking Tool is a lightweight and cross-platform application that has the capacity to scan the IP addresses in any range and also in their ports. The Hacking Tool simply pings each IP address.
Features:
- Scans local networks as well as the Internet
- The free and open-source tool
- Random or file in any format
- Exports results in many formats
- Extensible with many data fetchers
- Provides command-line interface
- Works on Windows, Mac, and Linux
- No need for Installation
13. SQLMap
SQLMAP is a cool cyber-security hacking tool written in Python that helps security researchers to launch SQL code injection tests against remote hosts.
With SQLMap hacking tool you can detect and test different types of SQL-based vulnerabilities to harden your apps and servers, or to report vulnerabilities to different companies.
Features:
- Multiple database server support: Oracle, PostgreSQL, MySQL and MSSQL, MS Access, DB2 or Informix.
- Automatic code injection capabilities
- Password hash recognition
- Dictionary-based password cracking
- User enumeration
- Get password hashes
- View user privileges and databases
- Database user privilege escalation
- Dump table information
- Executes remote SQL SELECTS
14. OpenVAS

OpenVAS Hacking Tool (also known as the old classic “Nessus”) is an open-source network scanner used to detect remote vulnerabilities in any host.
One of the best-known network vulnerability scanners. This Hacking Tool is very popular among system administrators and DevOps and infosec professionals.
Features:
- Powerful web-based interface
- +50,000 network vulnerability tests
- Simultaneous multiple host scanning
- Able to stop, pause and resume scan tasks
- False-positive management
- Scheduled scans
- Graphics and statistics generation
- Exports results to plain text, XML, HTML or LateX
- Powerful CLI available
- Fully integrated with Nagios monitoring software
- While its web-based interface allows it to be run from any operating system, a CLI is also available and works well for Linux, Unix, and Windows operating systems.
15. Medusa

Medusa is one of the best online brute-force hacking tools speedy, parallel password crackers that are available on the Internet. This Hacking Tool has been designed by the members of the website foofus.net.
Features:
- It is designed in such a way that it is speedy, massively parallel, modular, login brute-forcer
- The main aim of this tool is to support as many services which allow remote authentication
- Allows to perform thread-based parallel testing and Brute-force testing
- Flexible user input. It can be specified in a variety of ways
- All the service module exists as an independent .mod file.
- No modifications are needed to the core application to extend the supported list of services for brute-forcing.






1 Comment
Hacking apk all games hack mod in 1 apk