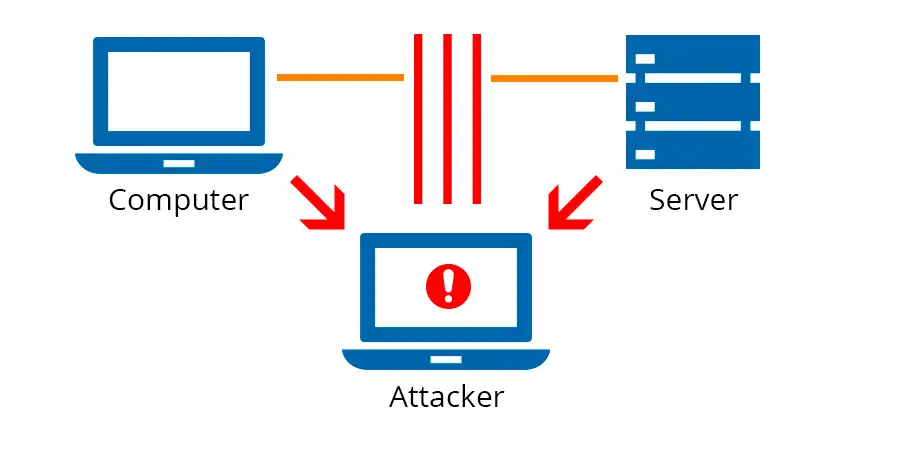
Man in the Middle Attack(MITM) intercepts communication between two systems where communication between two users is monitored and modified by an unauthorized party.
For eg., Data is sent from point A (computer) to point B (server/website), and an attacker can get in between these transmissions.
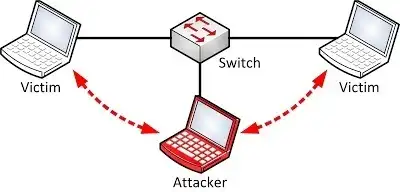
They then set up tools programmed to “listen in” on transmissions, intercept data that is specifically targeted as valuable, and capture the data.
Man in Middle Attacks can happen in any form of online communication, such as email, social media, web surfing, etc.
Not only are they trying to eavesdrop on your private conversations, but they can also target all the information on your devices.
The goal of a Man in the Middle Attack(MITM) is to steal personal information, such as login credentials, account details, and credit card numbers.
Sometimes this data can be modified in the process of transmission to try to trick the end user to divulge sensitive information, such as login credentials.
In the Man in the Middle Attack(MITM) process, the two original parties appear to communicate normally.
The message sender does not recognize that the receiver is an unknown attacker trying to access or modify the message before retransmitting it to the receiver. Thus, the Man in Middle Attacker controls the entire communication.
The most common (and simplest) way of doing a Man in the Middle Attack is a passive attack in which an attacker makes free, malicious WiFi hotspots available to the public.
Typically named in a way that corresponds to their location, they aren’t password protected. Once a victim connects to such a hotspot, the attacker gains full visibility to any online data exchange.
The Man in the Middle Attack is very effective because of the nature of the HTTP protocol and data transfer which are all ASCII based.
From Man in the Middle Attack, it’s possible to view an interview within the HTTP protocol and also in the data transferred.
A newer variant of Man in the Middle Attack has been gaining popularity with cybercriminals due to its ease of execution.
With a man-in-the-browser attack, an attacker needs a way to inject malware into the computer, which will then install itself into the browser without the users’ knowledge, and will then record the data that is being sent between the victim and specifically targeted websites, such as financial institutions, that are coded into the malware.
Once the malware has collected the specific data it was programmed to collect, it then transmits that data back to the attacker.
Connection Susceptible to Man in the Middle Attack
- Financial sites between login and authentication
- Connections meant to be secured by public or private keys
- IP spoofing
- ARP spoofing
- Sidejacking
- Sniffing
- DNS spoofing, also known as DNS cache poisoning
- Other sites that require logins where there is something to be gained by having access
How to Prevent Man in the Middle Attack (MITM)
- Avoiding WiFi connections that aren’t password protected.
- Make sure “HTTPS” is always in the URL bar of the websites you visit.
- Be wary of potential phishing emails from attackers asking you to update your password or any other login credentials.
- Instead of clicking on the link provided in the email, manually type the website in question address into the URL bar of your browser and proceed from there.
- Be sure that your home network is secured.
- Paying attention to browser notifications reporting a website as being unsecured.
- Immediately logging out of a secure application when it’s not in use.
- Not using public networks (e.g., coffee shops, and hotels) when conducting sensitive transactions.