A zombie computer or network is a collection of compromised computers or hosts connected to the Internet that’s been infected by a computer virus or malicious program.
A computer is under the control of a malicious hacker without the knowledge of the computer owner and uses it to conduct illegal activities. zombie computers are often used to spread e-mail spam and launch Distributed denial-of-service attacks (DDOS attacks). Once your system has been turned into a zombie it’s helping to make the Internet a more dangerous place.
zombie computer sends an enormous amount of packets of useless information to a targeted Web site in order to clog the site’s routers and keep legitimate users from gaining access to the site.
A zombie computer can appear to be performing normally, making it hard for you to know that your computer has been compromised. Over time, however, most zombie computers accumulate so much malware that they become unusable by their owners.
The purpose is usually either financial gain or malice. Attackers typically exploit multiple computers to create a botnet. The most typical use of botnets is for widely disseminating spam (unwanted commercial e-mail), which makes it difficult to determine the original spammer. The hacking tools used to establish hidden control in a remote computer are referred to as a rootkit.
Individual zombie computers have been used to store and transmit child pornography and other illegal materials. The hacker can control the zombies by broadcasting single commands, negating the need to communicate with each target individually.
Symptoms of Zombie Computer
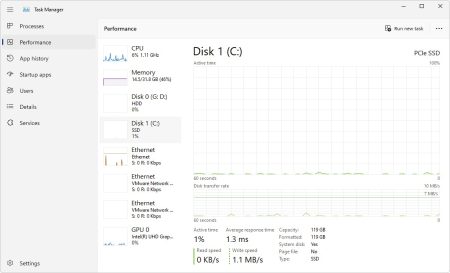
- Your computer is slowing down: Your computer’s performance is noticeably slower, even when you don’t have many applications open.
- Your computer crashes frequently.
- Unfamiliar messages in outgoing mail or bounced return mail not sent by you.
- You receive unexplained error messages.
- It takes your computer longer to shut down and start-up.
- Your access to computer security websites is blocked.
- Sudden pop-up windows opening and closing.
- You can’t access the Control Panel.
- Everything seems to work perfectly on your PC.
- Suspicious or unknown apps installed on the PC
How to Remove Zombies from your computer
- Update your antivirus and/or anti-spyware software and scan your computer’s hard drive to find and remove the malware. Keep in mind some types of malware will prevent your antivirus software from running.
- Set your computer’s personal firewall to its maximum-security level.
- Often, zombie/bot malware hides from security software scanners by installing a rootkit. A rootkit is a stealth piece of software that’s usually malicious.
- If you can’t remove zombies from these steps then you should completely wipe the hard drive or flash drive and reinstall the operating system and applications. Make sure your important files are backed up first, of course.