A botnet is a collection of internet-connected devices in a coordinated fashion for malicious purposes. Each computer in a botnet is called a bot.
Bots are also known as “zombie computers” due to their ability to operate in remote directions without their owners’ knowledge.
These are networks made up of remote-controlled computers, or “bots.” These computers have been infected with malware that allows them to be remotely controlled.
Some botnets consist of hundreds of thousands or even millions of computers.
It has become one of the biggest threats to security systems today. The word Botnet is formed from the words ‘robot’ and ‘network’.
In a broad sense, that’s exactly what botnets are: a network of robots used to commit cybercrime.
The cybercriminals controlling them are called botmasters or bot herders. Botnets can be used to perform distributed denial-of-service attacks (DDoS attacks), steal data, send spam, and allow the attacker to access the device and its connection.
The owner can control the botnet using command and control (C&C) software. The botnet is an example of using good technologies for bad intentions.
You need to be careful of are the illegal and malicious botnets. When botnets gain access to your machine through some piece of malicious coding.
Basically, botnets were created as a tool with valid purposes in Internet relay chat (IRC) channels.
Eventually, hackers exploited the vulnerabilities in IRC networks and developed bots to perform malicious activities such as password theft, keystroke logging, etc.
Botnets are also becoming a larger part of cultural discussions around cybersecurity. These aren’t typically created to compromise just one individual computer; they’re designed to infect millions of devices.
Bot herders often deploy botnets onto computers through a trojan horse, virus. Botnets are difficult to detect.
Using methods and tools that can be found online in minutes, a botnet creator can create a central command and control server and then use social engineering to inject malware onto the victim’s computer
Architecture of Botnet
Basically bot programs are constructed as clients which communicate via existing servers. This allows the bot herder (the person controlling the botnets) to perform all control from a remote location, which obfuscates their traffic.
Many recent botnets now rely on existing peer-to-peer networks to communicate.
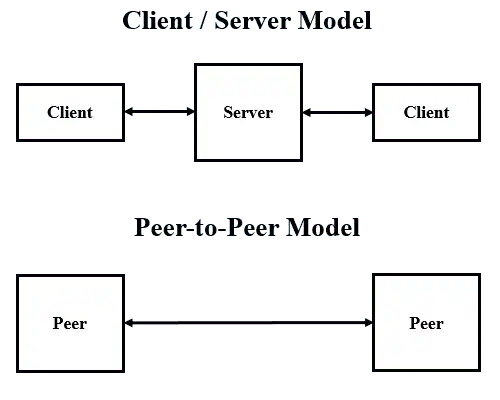
- Client-server model- The client-server botnet structure is set up like a basic network with one main server controlling the transmission of information from each client. the client-server model works well for taking and maintaining control over the botnet.
- Peer-to-peer- In this newer botnets have evolved to use the more interconnected peer-to-peer (P2P) structure. In a P2P botnet, each infected device functions as a client and a server. P2P botnet structures make it harder for law enforcement to locate any centralized source.
Is Installing Botnet Is Illegal
The installation of malware on the victim’s computer, without the victim’s consent, to build the botnet is illegal and the activity the botnet conducts may be illegal.






1 Comment
I am truly grateful to the holder of this web site who has shared this great paragraph at at this place.