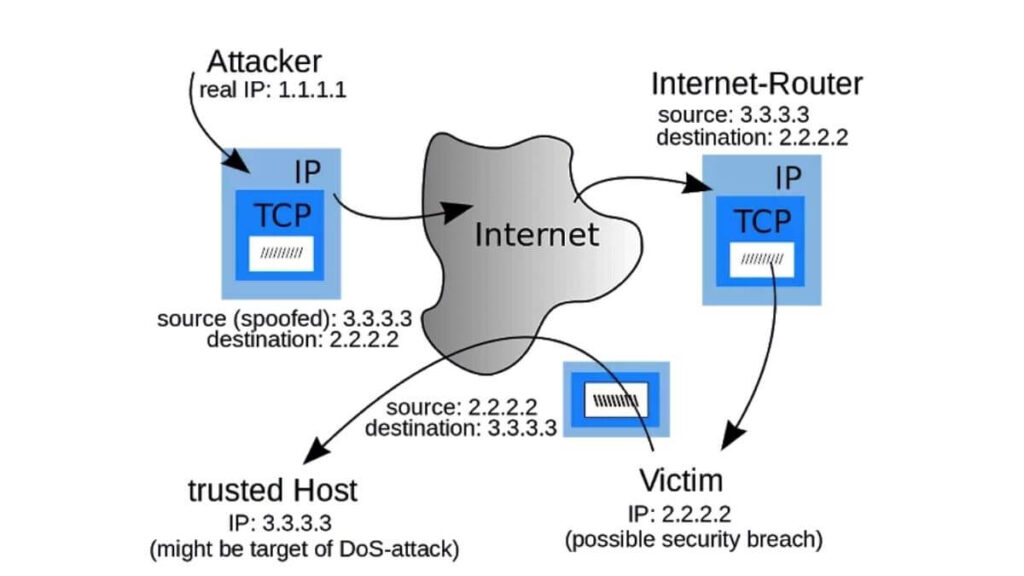
IP spoofing refers to connection hijacking through a fake Internet Protocol (IP) address with a false source IP address, for the purpose of hiding the identity of the sender or impersonating another computing system.
When a computer outside of your network pretends to be a trusted computer within the network, then, this action by the attacker is called IP Spoofing.
IP spoofing is also known as IP address forgery or a host file hijack. IP Spoofing involves modifying the packet header with a forged (spoofed) source IP address.
A hacker must first use a variety of techniques to find an IP address of a trusted host and then The hijacker obtains the IP address of a legitimate host and alters packet headers so that the legitimate host appears to be the source.
During this masking process, the fake IP address sends what appears to be a malevolent message coupled with an IP address that appears to be authentic and trusted.
IP spoofing involving the use of a trusted IP address can be used by network intruders to overcome network security measures, such as authentication based on IP addresses.
This type of attack is most effective where trust relationships exist between machines. To gain access to your network, an outside computer must gain one of your trusted IP addresses from the network.
So, the attacker might use an IP address within the range of your network. Or, on the other hand, the attacker can also use an authorized external IP address that is trusted within the network.
When IP spoofing is used to hijack a browser, a visitor who types in the URL (Uniform Resource Locator) of a legitimate site is taken to a fraudulent Web page created by the hijacker.
Criminals have long employed the tactic of masking their true identity, from disguises to aliases to caller-id blocking.
It should come as no surprise then, that criminals who conduct their nefarious activities on networks and computers should employ such techniques.
It aims to hijack computer sessions through denial-of-service attacks, which aim to overwhelm the victim with traffic.
Different ways of IP spoofing
- Injection of data or a set of commands into an existing stream of data that is passed in between a client and server application.
- Injection of data or commands into a peer-to-peer network connection.
Types of attacks implemented through the IP spoofing
- Blind Spoofing
- Non-Blind Spoofing
- Denial-of-service attack
- Man-in-the-middle attack