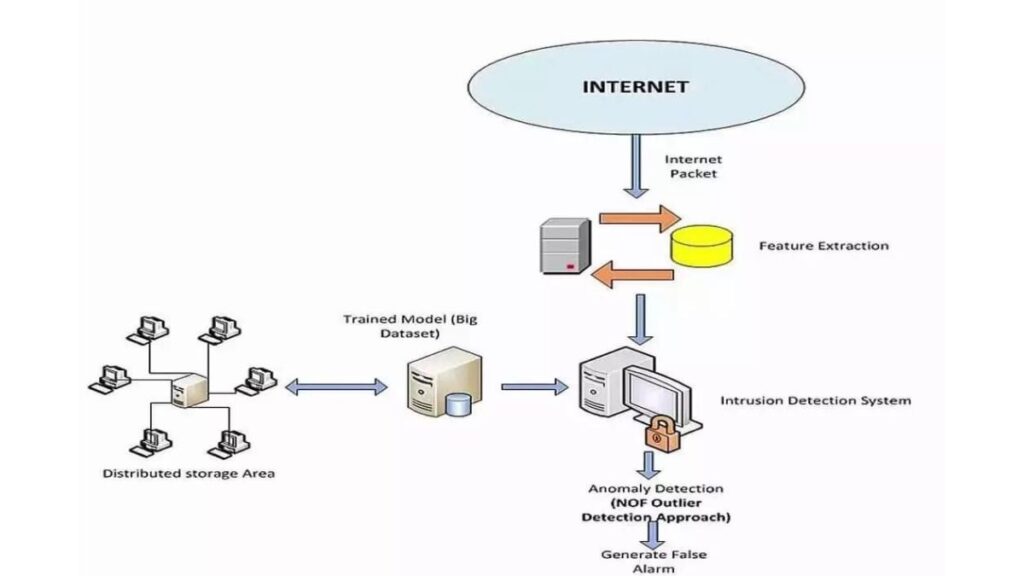
An IDS (Intrusion Detection System) is a device or software application that monitors network or system activities about unauthorized access as well as misuse.
IDS can be used to inspect network or host activity. An IDS evaluates a suspected intrusion once it has been taken and produces reports to a Management Station.
Intrusion detection systems (IDSes) are those that have recently gained a considerable amount of interest. An IDS is a defense system that detects hostile activities in a network.
The key is then to detect and possibly prevent activities that may compromise system security, or a hacking attempt in progress including reconnaissance/data collection phases that involve, for example, port scans.
One key feature of intrusion detection systems is their ability to provide a view of unusual activity and issue alerts notifying administrators and/or block a suspected connection.
Types of Intrusion Detection System
1. Network-Based IDS
A network-based intrusion detection system (NIDS) is used to monitor and analyze network traffic to protect a system from network-based threats.
A NIDS reads all inbound packets and searches for any suspicious patterns.
When threats are discovered, based on their severity, the system can take action such as notifying administrators, or barring the source IP address from accessing the network.
NIDS can most similarly be compared to a sniffer on steroids. Types of NIDS include Snort and Cisco NIDS.
NIDS may also be somewhat subject to an overabundance of focus. When a NIDS is closely following an event on a network in an attempt to discern whether or not it is an attack, other events may be granted a lesser level of attention.
These factors give the Zukin a few toeholds when attempting to evade a network IDS.
3. Host-Based IDS
HIDS is a bit different than NIDS in the aspect that it is run as a service or agent on the protected host.
HIDS does not inspect traffic that is not directed at the host it is protecting.
Instead, the HIDS agent monitors settings on the machine, like critical system files (/etc/password, the NT SAM file, etc), registry settings, file checksums, or just about any other parameters you define.
When an attack is made on a machine, the agent will typically block the connection, log a record of the session, report it back to a central management console, and of course alert the admin of the problem.
HIDS also has another distinct characteristic; it can inspect encrypted traffic because the traffic is actually decrypted before the agent inspects it.
NIDS, on the other hand, can’t do anything about encryption. Types of HIDS, include Tripwire, and Cisco HIDS.