WEP (Wired Equivalent Privacy) is an encryption algorithm used to secure wireless networks.
Wired Equivalent Privacy WEP is a security protocol, specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11b.
That is designed to provide a wireless local area network (WLAN) with a level of security and privacy comparable to what is usually expected of a wired LAN.
Wired Equivalent Privacy recognizable by its key of 10 or 26 hexadecimal digits (40 or 104 bits), was at one time widely in use and was often the first security choice presented to users by router configuration tools.
WEP is designed to provide the same level of security as that of a wired LAN. LANs are inherently more secure than WLANs because LANs are somewhat protected by the physicalities of their structure, having some or all parts of the network inside a building that can be protected from unauthorized access.
In 2003 the Wi-Fi Alliance announced that WEP had been superseded by Wi-Fi Protected Access (WPA).
In 2004, with the ratification of the full 802.11i standard (i.e. WPA2), the IEEE declared that both WEP-40 and WEP-104 have been deprecated.
The goal of WEP is to make wireless networks as secure as wired networks, such as those connected by Ethernet cables.
How Does WEP Work?
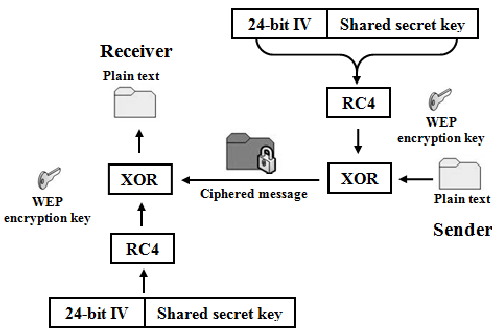
WEP uses the RC4 algorithm to encrypt the packets of information as they are sent out from the access point or wireless network card.
As soon as the access point receives the packets sent by the user’s network card it decrypts them.
The original implementations of WEP supported encryption keys of 40 bits plus 24 additional bits of system-generated data, leading to keys of 64 bits of total length Other supported encryption keys included the 128 and 256-bit variations.
The higher the number of bits – the longer the encryption key. Consequently, the harder it is for somebody to find the matching key and gain access to the Wi-Fi connection.
And with a bit of technical know-how – to the personal data transmitted over the network.
When deployed over a Wi-Fi connection, WEP encrypts the data stream using these keys so that it is no longer human-readable but still can be processed by receiving devices.
The keys themselves are not sent over the network but rather are stored on the wireless network adapter or in the Windows Registry.
Wired Equivalent Privacy Weakness
- The integrity of the packets is checked using Cyclic Redundancy Check (CRC32). A CRC32 integrity check can be compromised by capturing at least two packets. The bits in the encrypted stream and the checksum can be modified by the attacker so that the packet is accepted by the authentication system. This leads to unauthorized access to the network.
- WEP uses the RC4 encryption algorithm to create stream ciphers. The stream cipher input is made up of an initial value (IV) and a secret key. The length of the initial value (IV) is 24 bits long while the secret key can either be 40 bits or 104 bits long. The total length of both the initial value and secret can either be 64 bits or 128 bits long. The lower possible value of the secret key makes it easy to crack it.
- Weak Initial value combinations do not encrypt sufficiently. This makes them vulnerable to attacks.
- WEP is based on passwords; this makes it vulnerable to dictionary attacks.
- Keys management is poorly implemented. Changing keys, especially on large networks is challenging. WEP does not provide a centralized key management system.
- Initial values can be reused.
Despite all the work that has been done to improve the WEP system it still is a highly vulnerable solution.
Systems that rely on this protocol should be either upgraded or replaced in case a security upgrade is not possible. WEP was officially abandoned by the Wi-Fi Alliance in 2004