A rootkit is a collection of computer software that enables administrator-level access to a computer or computer network.
Utilizing a portion of the lower layers of the operating system (API work redirection, utilizing undocumented OS functions, etc.), makes them undetectable by common anti-malware software.
Once It is installed, it enables the attacker to mask intrusion and gain root or privileged access to access to the PC and, perhaps, different machines on the system.
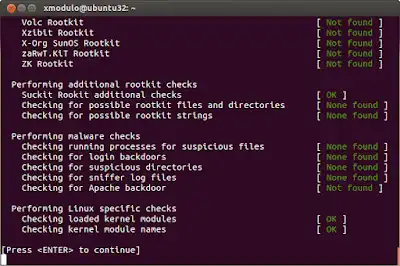
Rootkit identification is difficult because a rootkit may be able to subvert the software that is expected to discover it.
Detection strategies incorporate using an alternative and trusted operating system, behavioral-based techniques, signature filtering, distinction examining, and memory dump investigation.
Removal can be confused or for all intents and purposes incomprehensible, particularly in situations where the rootkit resides in the kernel; reinstallation of the operating system might be the main accessible answer for the problem.
When managing firmware rootkits, removal may require hardware replacement or specialized equipment.
The case of a rootkit on a system was first reported in the mid-1990s. Around then, Sun and Linux operating were thee system essential focuses for a program hoping to introduce a rootkit.
Today, rootkits are accessible for various working frameworks, including Windows, and are progressively hard to recognize on any system.
Also Read:
Please note that rootkits can be either legitimate or malicious. Correct rootkits may be installed as a part of the legitimate application.
The list of some well-known rootkits can be found in the Detection of known legitimate rootkits. Because of that, it is necessary to pay close attention to the Anti-Rootkit results.
A rootkit can get to a PC utilizing different ways. The most widely recognized path is through some trojan steed or some suspicious email connection.
Additionally surfing the web may bring about the establishment of a rootkit, for instance when an “exceptional” module (putting on a show, to be honest to goodness) is expected to effectively see some site page, dispatch some records, and so forth.