The NTP enumeration is a protocol for synchronizing time across your network, this is especially important when utilizing Directory Services.
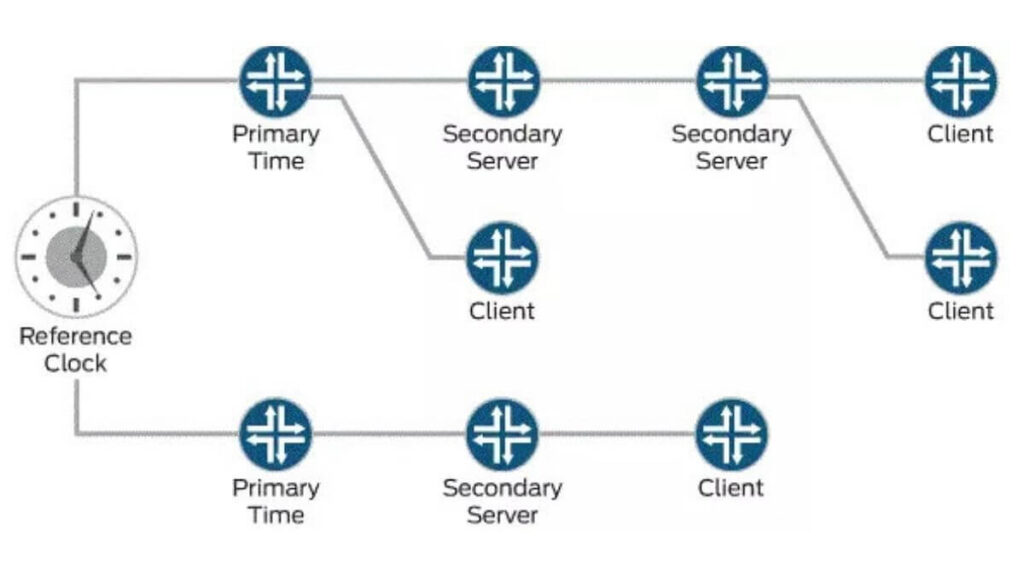
It can be implemented in various models like client-server and peer-to-peer.
The current version of NTP is ntpv4 and uses the User Datagram Protocol (UDP) and port number 123.
In a client-server model, the client sends a packet mode 4 to the server and the server responds back with a packet mode 3 and provides synchronization to them.
Also Read:
- Hacking Terminologies
- What is peer-to-peer Network(P2P)
- What is Scanning and Its Countermeasures
- What is Web Server and How do Web Server Works
There exists a number of time servers throughout the world that can be used to keep systems synced to each other. NTP utilizes UDP port 123.
Through NTP enumeration you can gather information such as lists of hosts connected to the NTP server, IP addresses, system names, and OSs running on the client system in a network.
All this information can be enumerated by querying the NTP server.
From a Vulnerability Analysis/ Penetration testing aspect, the data available when querying the NTP server can prove quite valuable and is usually available without any formal authentication being required. NTP Suite is used for NTP enumeration.
NTP enumeration is important because in a network environment, you can find other primary servers that help the hosts to update their times and you can do it without authenticating the system.
NTP enumeration Properties
- NTP enumeration can maintain time to within 10 milliseconds (1/100 seconds) over the public Internet.
- NTP enumeration can achieve accuracies of 200 microseconds or better in local area networks under ideal conditions.
- Attacker queries NTP server to gather valuable information such as:
- List of hosts connected to NTP server
- Clients’ IP addresses in a network, their system names, and OSs
- Internal IPs can also be obtained if the NTP server is in the DMZ,
Network Tim Protocol (NTP) Security Model
Intruders can play with this protocol to clog the network with big response packets (recent DDoS amplification attack), disrupt some time-dependent critical services, etc.
There are various types of attacks that are possible on NTP. Some of them are discussed below:
- A replay attack is in which an intruder replays one or more packets.
- Man in the middle attack (MITM) in which an intruder can intercept the packets between authentic client and server.
- A delayed attack in which packets between client and server are delayed for a constant or variable time but left unchanged.
- A DDoS attack in which an attacker finds a vulnerable machine makes it a botmaster and infects other vulnerable systems with malware. NTP DDoS is a type of reflective DDoS attack in which an attacker sends spoofed SYN packets so that when the server replies to the spoofed packet, replies go to the spoofed IP in the SYN packet.
- In DDoS, the amplification factor is used by attackers to increase the traffic volume in an attack. Results have shown that in an NTP DDoS attack, an attacker who has 1 GB of bandwidth can generate the attack with an amplification factor close to 250 GB. More on this will be covered later in this article.
NTP Enumeration Commands
ntptrace
- Traces a chain of NTP servers back to the primary source
- ntptrace [-vdn] [-r retries] [-t timeout] [server]
ntpdc
- Monitors operation of the NTP daemon, ntpd
- /usr/bin/ntpdc [-n] [-v] host1 | IPaddress1…
ntpq
- Monitors NTP daemon ntpd operations and determines performance
- ntpq [-inp] [-c command] [host] […]
Reference: https://www.juniper.net/documentation/images/g041686.gif