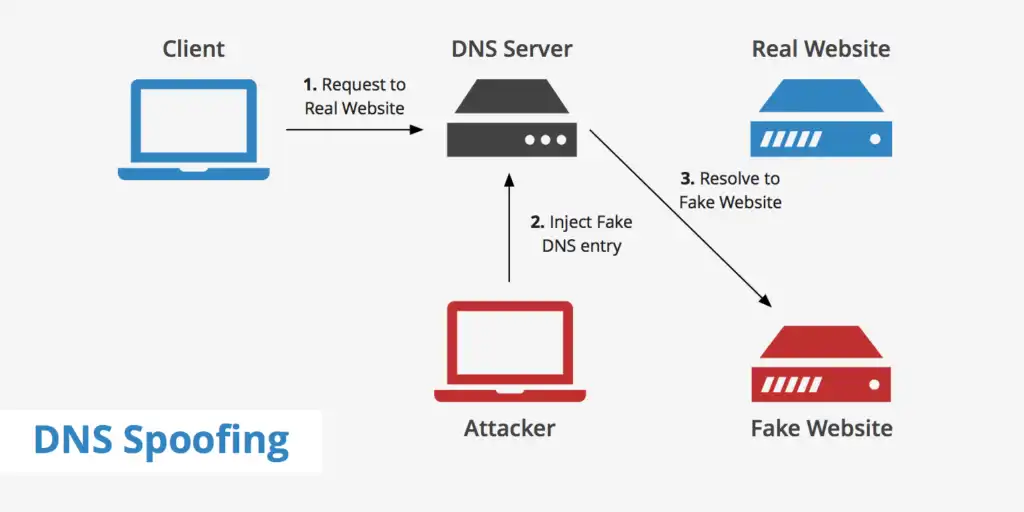
DNS Spoofing (sometimes referred to as DNS Cache Poisoning) is a process by which DNS server records are illegitimately modified to replace a website address with a different address.
DNS Spoofing is a type of computer attack where a user is forced to navigate to a fake website disguised to look like a real one, with the intention of diverting traffic or stealing the credentials of the users.
An attacker could redirect all DNS requests, and thus all traffic, to his (or her) machine, manipulating it in a malicious way and possibly stealing data that passes across.
This redirection of traffic allows the attacker to spread malware, steal data, etc.
When a web user looks for the affected page, the request is redirected to a different address where a worm, spyware, web browser hijacking program, or other malware can be downloaded to the user’s computer from the other location.
But Normal DNS communication occurs when the system requests the IP of a particular website and the DNS server responds back with the actual IP address of that website.
DNS spoofing is another one of the man-in-the-middle attacks that can force victims to navigate to a fake website purporting to be a real one.
The code for DNS cache poisoning is often found in URLs sent via spam emails. These emails attempt to frighten users into clicking on the supplied URL, which in turn infects their computer.
To perform a cache poisoning attack, the attacker exploits flaws in the DNS software. DNS spoofing can cause quite a bit of trouble both for website visitors and website owners.
An attacker’s main motive to carry out a DNS spoofing attack is either for their own personal gain or to spread malware.
Also Read:
- How to remove ransomware from Your PC
- What is DNS spoofing and how to Prevention It
- 5 Features You Should Look for in an Antivirus
Prevention Of DNS spoofing
- Secure your internal systems: the internal system must be kept secure and updated with the latest security patches from the different vendors.
- Maintain the DNS software Up-to-Date.
- SSL is a great defense along with IPsec.
- DNSSEC: DNSSEC is a very secure technology that can be used to allow only digitally signed DNS records to be published on DNS servers.
- Allow updates and zone transfers from trusted sources.
- Use Virtual Private Networks (VPNs)
- Encrypt your sensitive traffic using an encrypting protocol such as SSH or IPsec