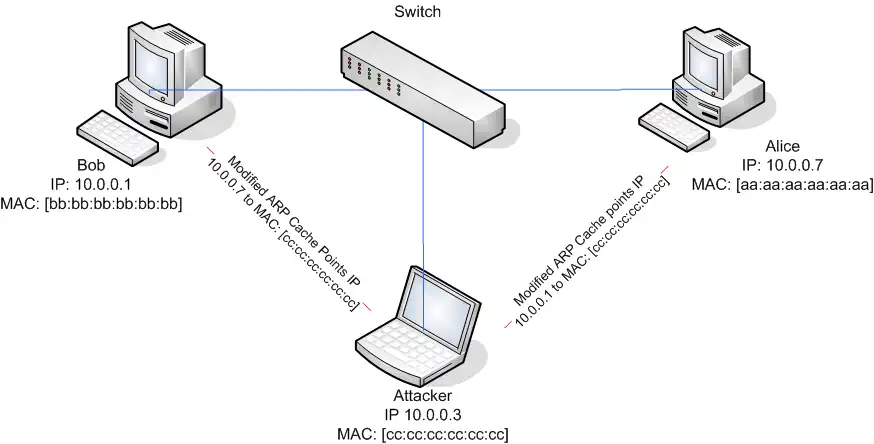
ARP spoofing (Address resolution protocol) is a technique that causes the redirection of network traffic to a hacker.
The basic principle behind ARP spoofing is to exploit the lack of authentication in the ARP, it is a type of attack in which attacker sends fake Address Resolution Protocol (ARP) messages inside a Local Area Network (LAN).
This results in the linking of an attacker’s MAC address with the IP address of a legitimate computer or server on the network. Through the LAN, the packets are being exchanged using the physical MAC addresses as the base network identifier rather than the IP addresses.
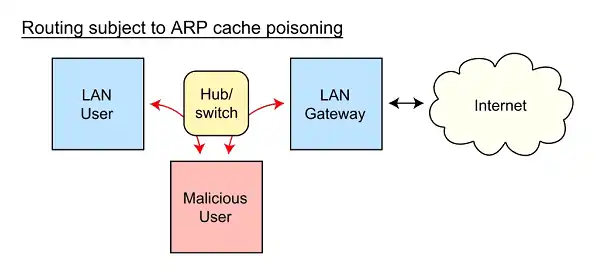
After the attacker’s MAC address is injected into a poisoned ARP table, any traffic sent to that IP address, will be routed to the attacker’s hardware instead of the real owner’s IP.
How does ARP spoofing work?
It is meant to steal some data intended for the target victim.
- The attack is usually launched using some tools.
- The attacker opens an ARP spoofing tool such as Arpspoof, Cain & Abel, Arpoison, and Ettercap and sets the IP address of the tool to match the IP subnet of the victim.
- Once the attacker sets the IP address to the IP subnet, it starts scanning the whole network to find out the IP address as well as the MAC address of all the hosts on the subnetwork.
- In the next step, a victim is targeted, and the attacker starts sending ARP packet across the Local Area Network (LAN), but the attacker replaces the MAC address of the target with its own MAC address while the IP address remains the same that of a victim.
- As discussed in the previous blog about ARP – the communication at the data link layer happens using the MAC address.
- So, the packets meant for the victim now gets rerouted to the attacker because the MAC address has been spoofed and replaced with the attacker’s MAC address.
- Once the attacker begins getting the packets meant for the victim, it can further launch different attacks.
ARP Spoofing Attacks
ARP spoofing attacks can have serious effects on enterprises. At their most basic level, these attacks are used to steal sensitive information from the company. Apart from this, this type of attacks is often used to facilitate other attacks like:
ARP Spoofing Detection, Prevention, and Protection
The following methods are recommended measures for detecting, preventing and protecting against these attacks:
- Packet filtering: Packet filters inspect packets as they are transmitted across a network. Packet filters are useful in ARP spoofing prevention because they are capable of filtering out and blocking packets with conflicting source address information (packets from outside the network that show source addresses from inside the network and vice-versa).
- Avoid trust relationships: Organizations should develop protocols that rely on trust relationships as little as possible. Trust relationships rely only on IP addresses for authentication, making it significantly easier for attackers to run ARP spoofing attacks when they are in place.
- Use ARP spoofing detection software: There are many programs available that help organizations detect ARP spoofing attacks. These programs work by inspecting and certifying data before it is transmitted and blocking data that appears to be spoofed.
- Use cryptographic network protocols: Transport Layer Security (TLS), Secure Shell (SSH), HTTP Secure (HTTPS) and other secure communications protocols bolster ARP spoofing attack prevention by encrypting data prior to transmission and authenticating data when it is received.
The techniques that are used in ARP spoofing can also be used to implement redundancy of network services. For example, some software allows a backup server to issue a gratuitous ARP request in order to take over for a defective server and transparently offer redundancy.
Image Source: Wikimedia